SSH is used to establish a secure connection between two computers, one local and one remote. While SSH is most often used for secure terminal access and file transfers, it may also be used to build a secure tunnel between machines in order to relay non-encrypted network connections. SSH tunnels can also be used to grant external access to internal network resources.
For example, while working on an IOT project for a client, I encountered a strange error. The error was related to an SSHException that occurred while publishing data to an AWS IOT topic.
I utilised Boto3 IoT data plane service to fix this error, and within this service, I used the publishing function to publish data to an AWS IOT topic.
Then I configured AWS ACCESS KEY, SECRET, and regions in AWS_ACCESS_KEY_ID, AWS_SECRET_ACCESS_KEY, and AWS_DEFAULT_REGION environment variables respectively
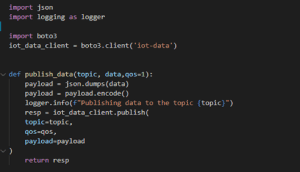
This code snippet is used to publish the data
The default security in the older version of the Boto3, i.e., Boto, was false. To eliminate this ambiguity, the above-mentioned code may function well with boto. However, if you have upgraded your Boto, security is enabled by default, and the code will give you this error:
“botocore.exceptions.SSLError: SSL validation failed for https://data.iot.us-east-2.amazonaws.com/topics/{your_topic}”
Then you will find the solution online and you will get a solution to this problem can be to set verify kwargs of the AWS IoT Client to false as shown below:
iot_data_client = boto3.client(‘iot-data’,verify = False)
But as soon as you execute it, you will start getting warnings like:
“Unverified HTTPS request is being made to host ‘data.iot.us-east-2.amazonaws.com’. Adding certificate verification is strongly advised.”
This creates a security warning and allows you to quickly modify your message in transit since it disables certificate verification and so does not transfer data via Shs. So, in order to address the problem, you must go through the debugging procedure.
What exactly do you mean by the debugging process, and why is it important to go through software testing?
Debugging is the process of detecting and removing existing and potential errors in a software code that may cause it to behave unexpectedly or to crash.
When I started debugging the above SSH Error and tried to figure out the difference, I came to know about a condition for accessing AWS IOT Data Plain Service and the condition were to access the data plane service of AWS IoT.
For example, in my case, I was trying to publish a message to an AWS topic and I need to provide a root CA certificate from an AWS authorized CA. The detailed description is given at the below-mentioned URL:
https://docs.aws.amazon.com/iot/latest/developerguide/server-authentication.html
As explained in the endpoint type section of the above URL, I downloaded the Verisign certificate. I was sending data to data.iot.us-east2 instead of using my own endpoint URL which I got from the AWS IoT Service Settings section. And for this reason, our endpoint fell into the iot: data type, and therefore, I selected the Verisign option.
Otherwise, I could have gone with the Amazon Trust Services Certificate, because it would fall into the iot:data-atts type endpoint.
Why I Preferred Amazon Trust Services Certificate?
- Eliminates the manual processes associated with using and managing SSL/TLS certificates.
- Certified private keys are protected and stored using strong encryption
- Handles automatic certificate renewal, and
- Avoids downtime due to incorrectly configured, revoked, or expired certificates.
Therefore, I downloaded the certificate from Verisign certificate URL which is mentioned in the link above, and also kept this certificate in a file named verisign_class_3_public_cert.pem. After this, I set the absolute path of this file in verify Kwargs of Boto3 client.
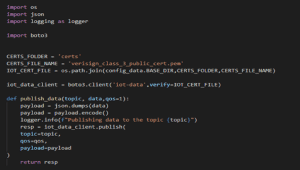
refer our code snippet to set an absolute path
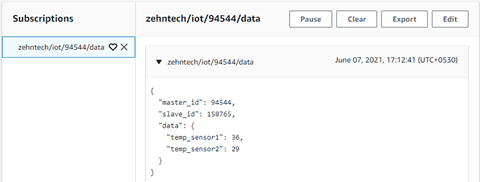
Finally, after executing the whole process step by step, I managed to publish a message on SSH on the topic AWS IoT as you can see in the image below: –
A place for big ideas.
Reimagine organizational performance while delivering a delightful experience through optimized operations.

Conclusion
The AWS Secure Tunneling component enables you to use AWS IoT Secure Tunneling to establish secure bidirectional communication with Greengrass Core devices that are behind restricted firewalls. Secure Tunneling uses MQTT over WebSockets to make these connections and it has a various data plan and services that helps to publish data to an AWS IOT topic. So that you can open SSH connections to the device using the tunnel managed by AWS IoT.
You can also access AWS IoT through the AWS IoT Console, which provides a graphical user interface (GUI) through which you can configure objects, certificates, rules, jobs, policies, and other elements of your IoT solutions. can manage.